In the last posts, you saw how to
Now, I will show you a way to block specific classifications from being sent with Exchange/O365 to other organizations. When a document is protected, some properties are added to the file. An exchange rule can detect them and react on them. For example, if the e-mail or an attachment contains a specific Azure Information Protection Label and is sent to a contact outside your organization, then you can block the message.

To get this behavior you must create two mail flow rules in your exchange environment. The first one is to block attachments, which have the specific classification set. The classification is stored in a property called Sensitivity. Your rule should look like that:

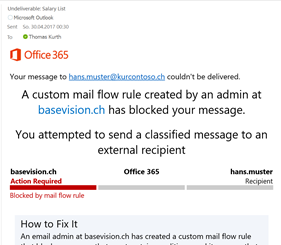
The second rule is to block messages, which have a specific classification in their mail header. The classification and many other Azure Information properties are stored in a mail header called msip_labels.
msip_labels: MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_Enabled=True; MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_SiteId=972e7678-7df2-4d6b-b297-e62aaa6971f0; MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_Ref=https://api.informationprotection.azure.com/api/972e7678-7df2-4d6b-b297-e62aaa6971f0; MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_SetBy=thomas.kurth@basevision.ch; MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_SetDate=2017-04-23T11:25:00.9564746+02:00; MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_Name=Confidential; MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_Application=Microsoft Azure Information Protection; MSIP_Label_40e837e6-3da8-45aa-97d8-ce91cde76b47_Extended_MSFT_Method=Manual; Sensitivity=Confidential
Because there is much more information in this property, we have to use the match operator. You can just search for the Label Name or you can specify “Sensitivity=Confidential” as the value.
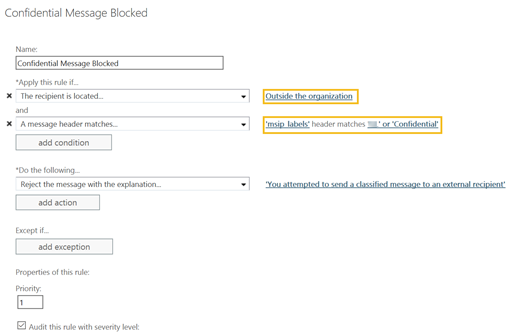
After activating these two rules, your users can no longer send classified documents to other organizations.
After protecting your Data, you would like to see how you can monitor and react to thefts. Stay tuned and follow me on twitter @ThomasKurth_CH to get an update, when the next post of this series is online.
- Microsoft Sentinel ASIM Parser demystified - March 31, 2024
- Enhancing Network Security Insights with IDS/IPS of Ubiquiti Dream Machine Pro and Microsoft Sentinel - March 10, 2024
- Ubiquiti Dream Machine Pro Logs to Microsoft Sentinel - February 6, 2024



0 Comments