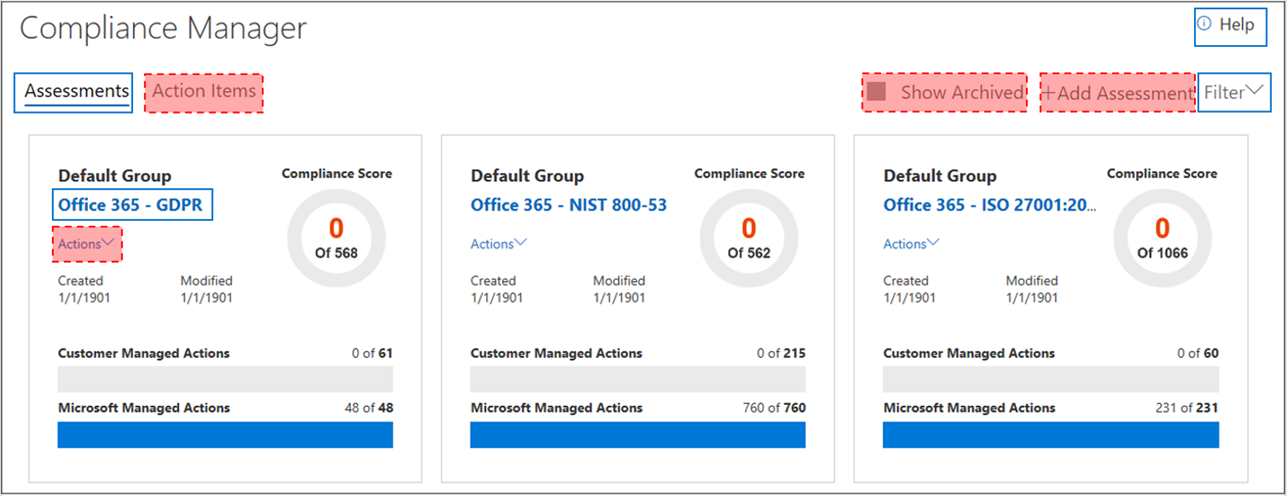
By default, everyone in your organization with an Office 365 or Azure AD account has access to Compliance Manager and can perform any action in Compliance Manager. So every company with an O356 subscription or Azure AD is probably giving insights to their defense strategy if they are using the Compliance Manager. First of all, for the people which do not know the Compliance Manager:
Compliance Manager, a workflow-based risk assessment tool in the Microsoft Service Trust Portal, enables you to track, assign, and verify your organization’s regulatory compliance activities related to Microsoft cloud services, such as Microsoft Office 365, Microsoft Dynamics 365, and Microsoft Azure. It gives the ability to track activities regarding NIST, ISO or GDPR and is helpful to start working on these topics. The main benefit is, that you can not only track your activities, also Microsoft is publishing their results including confidence through third parties.
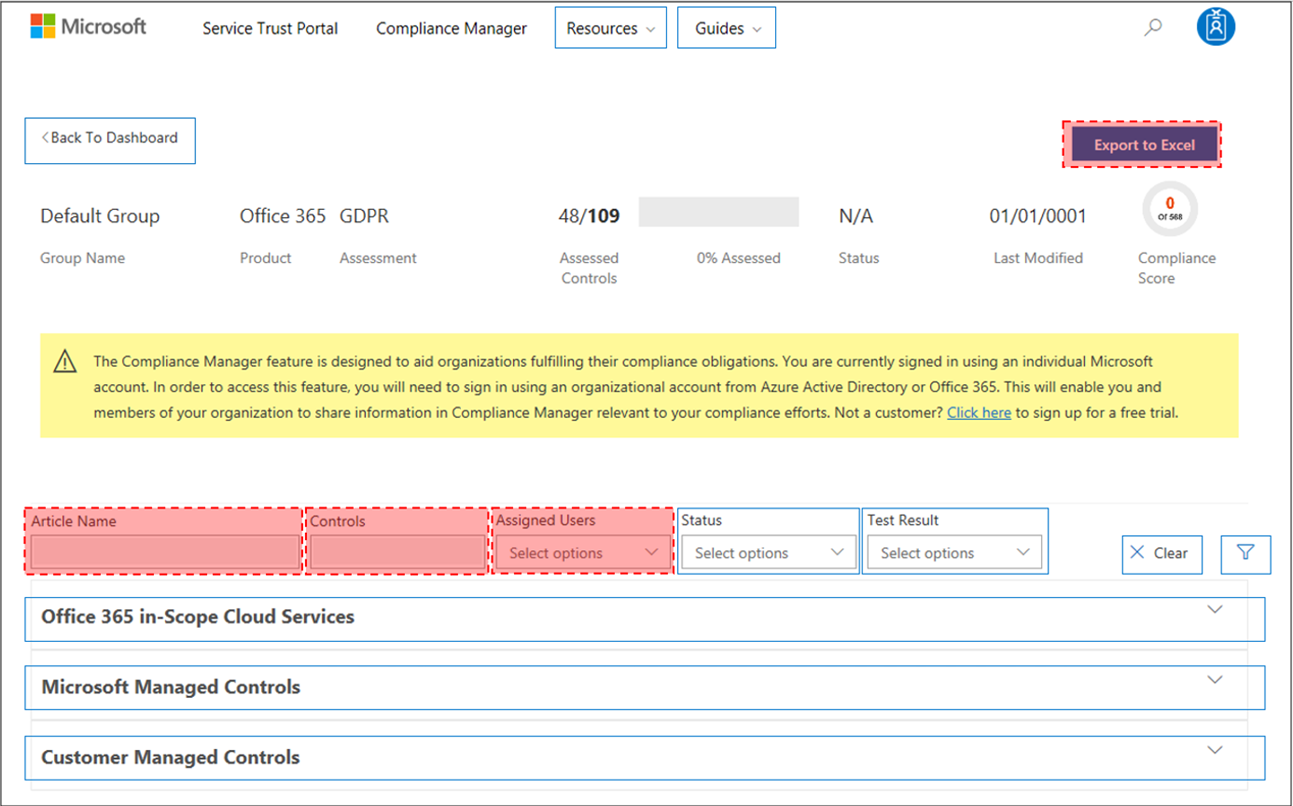
At the end the users without a role will still be able to access the service trust portal but will only see the information provided by Microsoft as you can see on the screenshot from docs.microsoft.com bellow. Red areas are inaccessible for users without a role assigned.
Take action to only allow specific users accessing the portal and hide confidential information for others
To change from default permissions to the role-based access control model, at least one user must be added to each Compliance Manager role (see the following instructions).
Important is also, that you cannot assign the permissions to an Azure AD group. You have to specify single users.
| Navigate to https://servicetrust.microsoft.com. | |
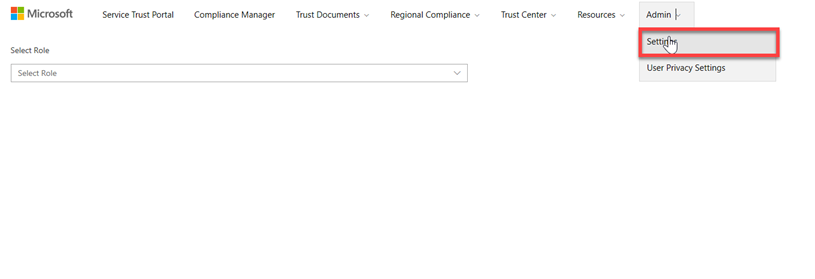 |
Open the settings page. |
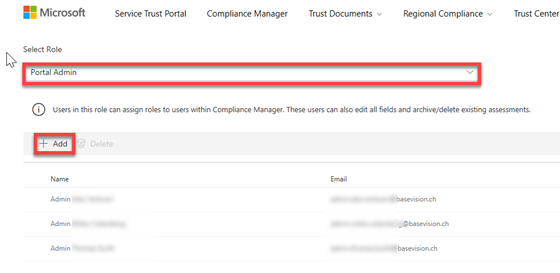 |
Select each role from the dropdown and specify dedicated user accounts from your directory. |
| Now only the defined people have access to the confidential information. |
I hope this blogs helps you to secure your environment. If you have any feedback, don’t hesitate to contact me.
- Microsoft Sentinel ASIM Parser demystified - March 31, 2024
- Enhancing Network Security Insights with IDS/IPS of Ubiquiti Dream Machine Pro and Microsoft Sentinel - March 10, 2024
- Ubiquiti Dream Machine Pro Logs to Microsoft Sentinel - February 6, 2024



0 Comments