During an Windows 10 / MDM / Syntaro project we faced an issue regarding MFA (Multi Factor Authentication). The customer was a local school where not all students have a smartphone during the class. Because of this, we had the requirement to disable MFA in his environment for Azure AD Joins.
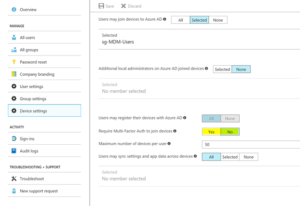
Our first idea was to simply disabled the requirement for MFA in the Azure AD Device Settings blade :). But we experienced that the problem was not solved with this change. The Azure AD Join still triggers an MFA.
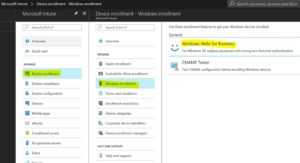
This means, that this is not the single setting, which will impact this behavior. We did some researches and found the feature, which triggers the MFA: Windows Hello for Business. The customer has enabled the automatic enrollment to Intune and configured there the Windows Hello for Business settings. To configure a device for Windows Hello an MFA is required. So, we had to disable Windows Hello for business and the MFA Requirement on Azure AD Join. Starting from this moment an Azure AD Join no longer requires an MFA.
I hope this post will help you in your future projects with the great EMS tools.
- Microsoft Sentinel ASIM Parser demystified - March 31, 2024
- Enhancing Network Security Insights with IDS/IPS of Ubiquiti Dream Machine Pro and Microsoft Sentinel - March 10, 2024
- Ubiquiti Dream Machine Pro Logs to Microsoft Sentinel - February 6, 2024




0 Comments